If you are looking for NFC blank stickers, Xinyetong is the right place. This Ntag213 NFC Blank Sticker, we will recommend, has higher performance and better price.
Ntag213 Blank RFID sticker has two main characteristics: white and embedded Ntag213 chip. With a white surface, no printing means it will be cheaper than the printed one. Another benefit is that some of NFC blank stickers support for reprinting, and you can print the appropriate pattern as needed. The Ntag213 chip is the connotation and core of this NFC blank sticker, which gives it the vitality of NFC technology, enabling it to achieve many functions, such as access control, social interaction, tracking, payment, etc.
We offer customized services, and you can tell us what kind of NFC blank sticker you need, including chip, size, shape, and other requirements. Here are some common NFC blank stickers as follows.
| Available Shape | Commonly Used Size | Available Chip |
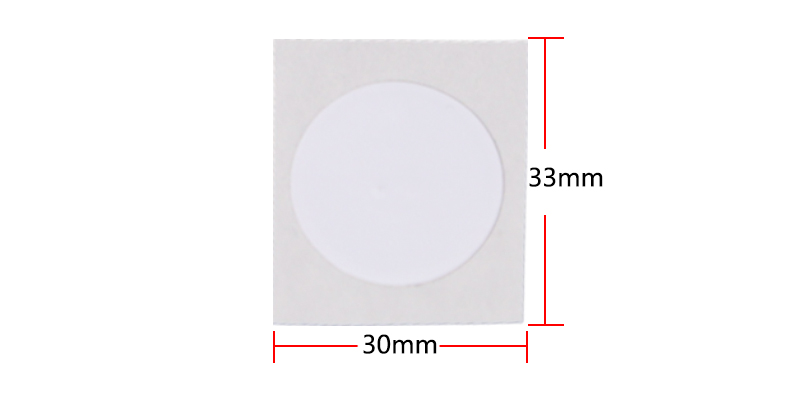 | 30*33mm | Ntag213, Ntag215, Ntag216 |
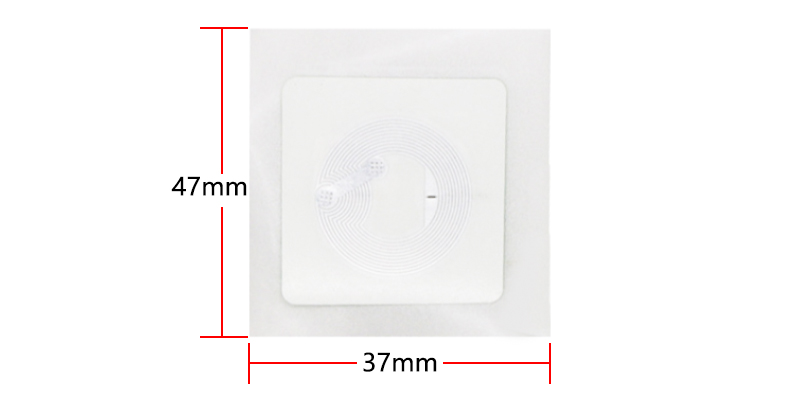 | 37*47mm | Ntag213, Ntag215, Ntag216 |
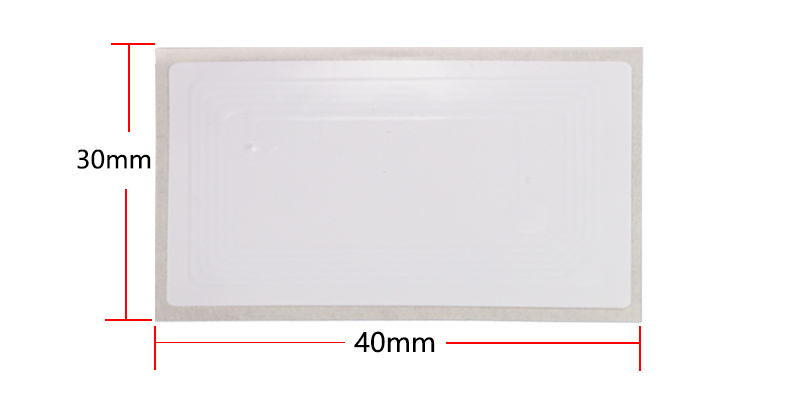 | 30*40mm | Ntag213, Ntag215, Ntag216 |
| Item | NFC Ntag213 bubble sticker |
| Chip | NTAG213 |
| Frequency | 13.56MHz |
| Protocol | ISO14443A |
| Size | 18*18mm, 30*30.5mm, 35*35mm, 42*42mm, 45*18mm,etc. |
| Memory | 144 bytes |
| Reading distance | 0-10cm |
| Write Endurance | 100000 times |
| Working Temperature | -25–65℃ |
| Data Retention Time | 10 years |
| Printing Options | Silk-screen printing, Laser Engraving, CMYK full color, Pantone, etc. |
| Crafts Available | Logo or number printing, Bar code, QR code, etc. |
| Samples | Free samples are available upon request |